Taking up the Gauntlet – SS7 Attacks in Ukraine
There have been several recent reports in the media on the results of new research into SS7 network. This interesting research outlines a series of techniques potential attackers can use to listen in to and read the calls and text messages of others. An obvious question for those of us in the telecom security industry is whether the threat is real and what we should do to address it. In considering an answer, we can look at a little-reported incident that occurred in Ukrainian Mobile networks earlier this year.
Last May, a report was issued by the Ukrainian Telecom Regulator (NKRZI[1]). This document, which went essentially unreported by the press outside of Ukraine & Russia, contains the result of the investigation of the NKRZI, assisted by the Ukrainian Security Service (SBU), into telecom network activity over several days in MTS Ukraine. The key findings of this report were that over a 3 day period in April 2014, a number of Ukrainian mobile subscribers were affected by suspicious/custom SS7[2] packets from telecom network elements with Russian addresses, causing their location and potentially the contents of their phone calls to be obtained.
The ’attacks’ outlined in the document involved SS7 packets being sent between the mobile operators. Without going into specific details, what occurred is a series of SS7 packets were received by MTS Ukraine’s SS7 network which modified control information stored in network switches for a number of MTS Ukraine mobile users. In doing so, when one of the affected mobile subscribers tried to ring someone else, their call would be forwarded to a physical land line number in St. Petersburg, Russia, without their knowledge – in effect the call has been intercepted. There is an additional further step that could be taken for the interception, not outlined in the original Ukrainian report, but suggested by the Washington Post article. The forwarded-to number could have initiated a new call to the original targeted subscriber, and then conference in the intercepted call, thus allowing itself to listen in to the call without the participants being aware.
In the document, the investigation stated that the custom SS7 packets themselves came from links allocated to MTS Russia, the parent company of MTS Ukraine. The Ukrainian regulator then assigned responsibility for the nodes that generated the SS7 based on the origination addresses in the SS7 packets received. According to the report, some of the SS7 source addresses that originated the attack were assigned to MTS Russia, while others were assigned to Rostov Cellular Communications.
It’s important to keep in mind that this is the report from one side only, and it is stated that they “draw conclusions about the potential for the interference with operation of telecom networks on the part of the PSTN area in the Russian Federation” , however in the report the regulator felt that MTS Ukraine was not doing enough to maintain the privacy of subscribers locations and call forwarding routes. For its part, MTS Russia denied that the SS7 address used was under its control, thus leaving the ultimate instigator a mystery. Indeed, in subsequent follow-ups it was reported that MTS Ukraine was not alone of being at risk, as the Ukrainian Telecom Regulator stated at a later date that Astelit and Kyivstar – the other main Ukrainian mobile operators – also experienced ‘external interference’. Whilst we don’t have information on the exact subscribers affected, there have been examples of very sensitive phone calls being intercepted by unknown means within the region, when using non government issued cell-phones. It is purely speculation on our part, but the same SS7 techniques outlined in the report could have conceivably been used to help achieve these interceptions.
Looking forward, an unfortunate, but seemingly inevitable, side-effect of these techniques is that it will lead to countries that have been affected adversely by SS7 attacks to attempt to build their own capability, thus leading to an ‘SS7 arms-race’. This has already been experienced in Ukraine, where new legislation has been submitted that one media source stated will allow their security services to legally listen in turn to subscribers of foreign mobile operators, track their location and obtain ‘other’ information about the activity of subscribers. Taken to extremes between countries, this would lead to a form of ‘mutually assured surveillance’, with mobile operators and mobile phone users on both sides suffering.
The Ukrainian report, and the recent research that has been released, shows us that we have moved into uncharted territory. Yes, there is a threat, and it is real – as the above example shows – however it does require considerable technical expertise to do this level of network interference. Not only to run and operate SS7 nodes capable of doing this – but especially to gain access to the SS7 network in the first place. Plus the nature of the risk is very different: consider there are more users of the SS7 network worldwide than there users of the internet, yet the number of attacks on IP networks everyday dwarf what is known to occur over SS7. The SS7 network is working as designed, but ’bad actors’ are increasingly trying to exploit it, the real danger is that we assume that nothing can be done to fix the problem and it will just get worse as more ’bad actors’ try to get access. As has been said by others, as an industry we need to work together to define recommendations and implement solutions to detect and stop potential attacks, because defences are possible and can make a difference if deployed correctly.
This coordination is already well underway, and AdaptiveMobile are helping to contribute to this, but no-one should doubt the amount of work and effort that will be required to completely secure the SS7 network from organisations that would seek to exploit it. However, at the same time it would be a mistake for those using these techniques offensively to assume that their activities & methods have gone unnoticed. We are now entering the more public stage of a struggle in which the gauntlet was thrown down some time ago.
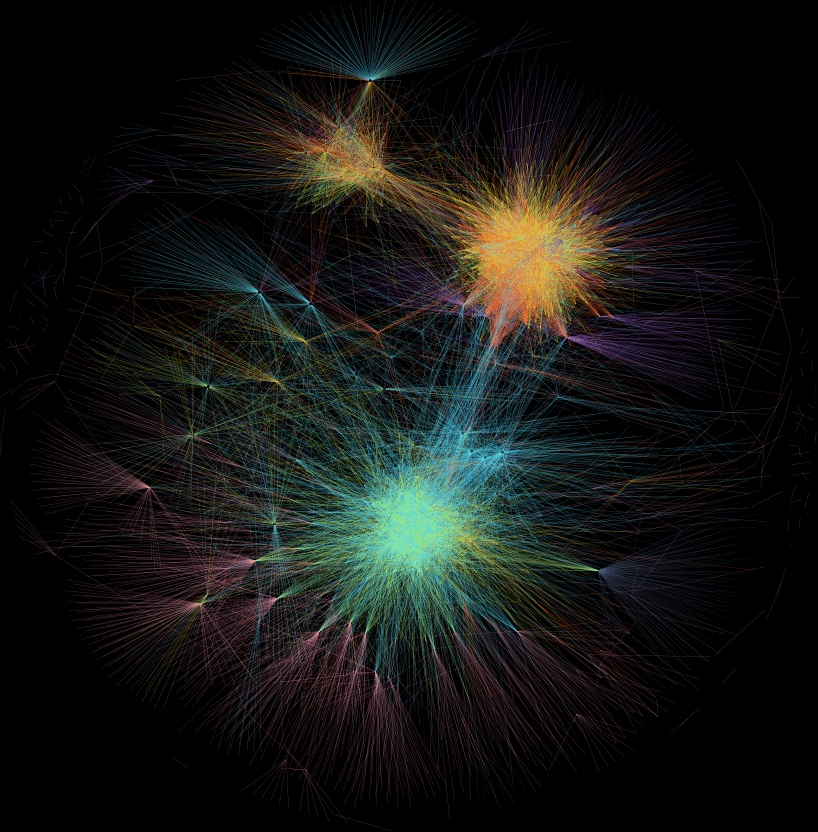
Example AdaptiveMobile visualisation of SS7 Activity between several mobile operators over a short time spam – looking for abnormal behaviour. Colours represent a selection of different SS7 packet types. The ’clumps’ are groups of similar SS7 node types. While unrelated to the events described in the report, the purpose of such work is to help investigate ways in which to detect malicious or unusual SS7 behaviour in networks. Such methods will be called on increasingly in the future to help detect and block unwanted SS7 activity.
Update : 3/1/2015
In the 3rd paragraph of the original blog entry on 16th of December, it was stated: ”In doing so, when someone tried to ring one of the affected mobile subscribers…” This has now been updated.
References:
[1] National Commission for the State Regulation of Communications and Information (Національна комісія, що здійснює державне регулювання у сфері зв`язку та інформатизації)
[2] Signalling System 7 (SS7), is a catch-all term for a telecom network technology that is used by hundreds of cellular companies to allow them to operate and communicate with each other; it is the computer protocol used by telecom nodes within cellular networks to provide mobility control, network registration, call and text setup etc. In short it enables mobile devices to communicate and roam globally, and it allows mobile operators to control and bill this activity. All pieces of network hardware that operate in the core network use SS7 to interoperate with the rest of the network.
